Nissan Hack! Aus & NZ Customers May be Targeted by Scammers

Author: James Greening
Nissan Oceania confirmed that its systems in Australia and New Zealand were affected by a cyber attack. The automaker has issued a notice to its consumers to be alert about unusual activity on their accounts and be patient with staff while it investigates the ‘cyber incident’.
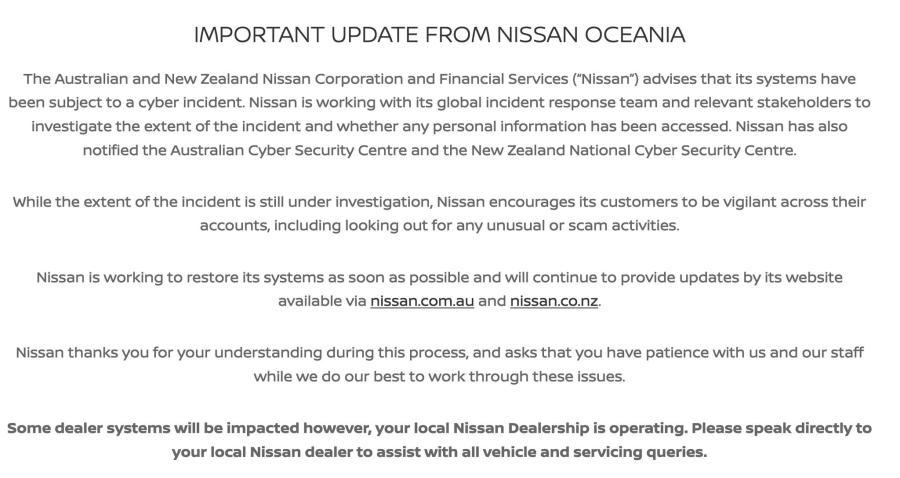
A statement posted on Nissan’s official website read, “The Australian and New Zealand Nissan Corporation and Financial Services (“Nissan”) advises that its systems have been subject to a cyber incident. Nissan is working with its global incident response team and relevant stakeholders to investigate the extent of the incident and whether any personal information has been accessed.”
Which Data Was Stolen in the Nissan Hack?
While the exact scope of the cyber attack on Nissan is not known, if recent data breaches on automakers are anything to go by, customer data such as names, addresses, email IDs, telephone numbers, location data, social security numbers and more may potentially have been stolen. Italian supercar manufacturer Ferrari confirmed earlier in the year that it was hit by a ransomware attack that exposed customers’ personal information such as names, addresses, email addresses and telephone numbers. However, Ferrari said no payment information or details of Ferrari cars owned or ordered had been stolen.
South Korean car manufacturer Hyundai also disclosed that it experienced a data breach a few months earlier and the data impacted by the breach included contact information (email, addresses and phone numbers) and vehicle data (such as chassis numbers).
Nearly 76,000 Tesla customers also lost their data to hackers when a whistleblower leaked confidential information to a German media outlet.The compromised information included names, contact information, social security numbers and employment-related records. The company supposedly offered credit monitoring and identity protection services to those affected
You May be a Target for Scams
Scammers equipped with nothing more than your name and contact information can already target you with a number of phone scams and email scams. Data leaked in hacks may include a lot more than basic information and you might be shocked at how cheaply stolen data is sold on the dark web. According to research, cybercriminals can start purchasing personally identifiable information (PII) on the dark web for as little as $15.
This trove of your personal information can be used to target you in sophisticated social engineering scams that can blind side even the most alert targets. Here are some of the most widespread scams that you need to watch out for:
Phishing Scams
Phishing exploits deceptive tactics to steal money by tricking individuals into divulging sensitive information like passwords or financial details. Cybercriminals often pose as trustworthy entities through fake emails or websites, urging victims to disclose confidential data.
To thwart phishing, scrutinise emails for red flags, verify sender legitimacy, avoid clicking on unfamiliar links, and use security features like two-factor authentication. Regularly update software and educate yourself about evolving phishing techniques. Vigilance and cautious online behaviour are crucial in preventing financial losses and protecting personal information from malicious actors.
Pig Butchering Scams (Crypto Catfishing Scams)
Pig butchering scams involve impostors creating fake online personas to manipulate individuals into fraudulent cryptocurrency transactions. These scammers build trust through false identities, often posing as experts or influencers in the crypto space.
To avoid falling victim, scrutinise online connections, verify identities through multiple channels and be wary of unsolicited investment advice. Avoid sharing personal or financial information with unknown individuals, use secure communication channels and prioritise reputable crypto platforms. Maintain a cautious approach to online interactions to mitigate the risks of pig butchering scams.
Sextortion Scams
Sextortion scams involve cybercriminals coercing victims into providing money or explicit content by threatening to expose compromising photos or information. Typically initiated through emails, messages, or social media, perpetrators exploit fear and embarrassment.
To avoid falling victim, refrain from sharing sensitive content with strangers, adjust privacy settings on social platforms and be sceptical of unsolicited requests.
If targeted, don't comply with demands, document evidence and report incidents to authorities. Maintain open communication with friends or family, and educate yourself about common scams. Vigilance, scepticism, and cautious online behaviour are essential in thwarting sextortion threats.
Always take the necessary precautions to safeguard your personal data but also remember that it can be stolen by hackers from third parties who have stored information about you. Always be alert with any kind of online or phone communication you receive as there is a fair chance that a scam may lurk behind it.
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
As the influence of the internet rises, so does the prevalence of online scams. There are fraudsters making all kinds of claims to trap victims online - from fake investment opportunities to online stores - and the internet allows them to operate from any part of the world with anonymity. The ability to spot online scams is an important skill to have as the virtual world is increasingly becoming a part of every facet of our lives. The below tips will help you identify the signs which can indicate that a website could be a scam. Common Sense: Too Good To Be True When looking for goods online, a great deal can be very enticing. A Gucci bag or a new iPhone for half the price? Who wouldn’t want to grab such a deal? Scammers know this too and try to take advantage of the fact. If an online deal looks too good to be true, think twice and double-check things. The easiest way to do this is to simply check out the same product at competing websites (that you trust). If the difference in prices is huge, it might be better to double-check the rest of the website. Check Out the Social Media Links Social media is a core part of ecommerce businesses these days and consumers often expect online shops to have a social media presence. Scammers know this and often insert logos of social media sites on their websites. Scratching beneath the surface often reveals this fu
How do I recover my crypto after it’s stolen? What happens if your crypto wallet is compromised? Can stolen crypto be traced, and can police actually recover crypto in 2026? These are the questions most people ask within minutes of realizing their wallet has been drained. Crypto theft is fast, quiet, and unforgiving. By the time most victims notice something is wrong, the funds are already moving across the blockchain. Once seen as a problem for exchanges and whales, crypto theft now heavily affects everyday investors. Phishing links, fake support chats, wallet approval scams, SIM swaps, and malware attacks have become common. Knowing what recovery realistically looks like—and what it doesn’t—can prevent panic, bad decisions, and costly follow-up scams. In a Nutshell Crypto recovery is possible, but only in limited situations Blockchain transactions are irreversible, but stolen crypto can still be traced Speed and documentation matter more than optimism Police and exchanges play a bigger role than private recovery services Guaranteed recovery offers are almost always scams Is it Actually Possible to Recover Stolen Crypto? Yes, crypto recovery is possible, but only under specific conditions and rarely through direct action by the victim. Blockchain transactions are final by design. Once crypto is sent and confirmed, it cannot be reversed. There is no central authority, no chargeback process, and no technical “undo” button, even if the transaction was clearly fraudulent. This is where many people ask whether stolen crypto can be traced. In most cases, it can. Every transaction
