Top 3 Twitter Scams 2022 — How to Avoid a Social Media Nightmare

Author: Trend Micro
This article is from Trend Micro.
Twitter scams are everywhere, and they’re really, really concerning. According to the FTC, last year social media was “a gold mine for scammers”, with more than one in four people who reported losing money to fraud saying the scam started on social media.
It’s not only money you could lose to these scams, either. If your Twitter account were to be compromised, you could lose memories, in the form of all the photos, videos, old Tweets, and personal messages linked to your account. You could lose your reputation too, because oftentimes when online accounts are compromised, they’re used to scam the victims’ friends and family.
To help you avoid a social media nightmare, we’ve compiled a list of three of the most common and clever Twitter scams that you need to know about.
STOP! Have You Enabled 2FA?
If you haven’t already, you should enable two-factor authentication (2FA) on your Twitter account for better security. For complete instructions on how to do so, click here.
#1 — Crypto-Related Scams
Such Twitter scams come in many forms, with the one commonality being that they all feature the theme of cryptocurrency in some way.
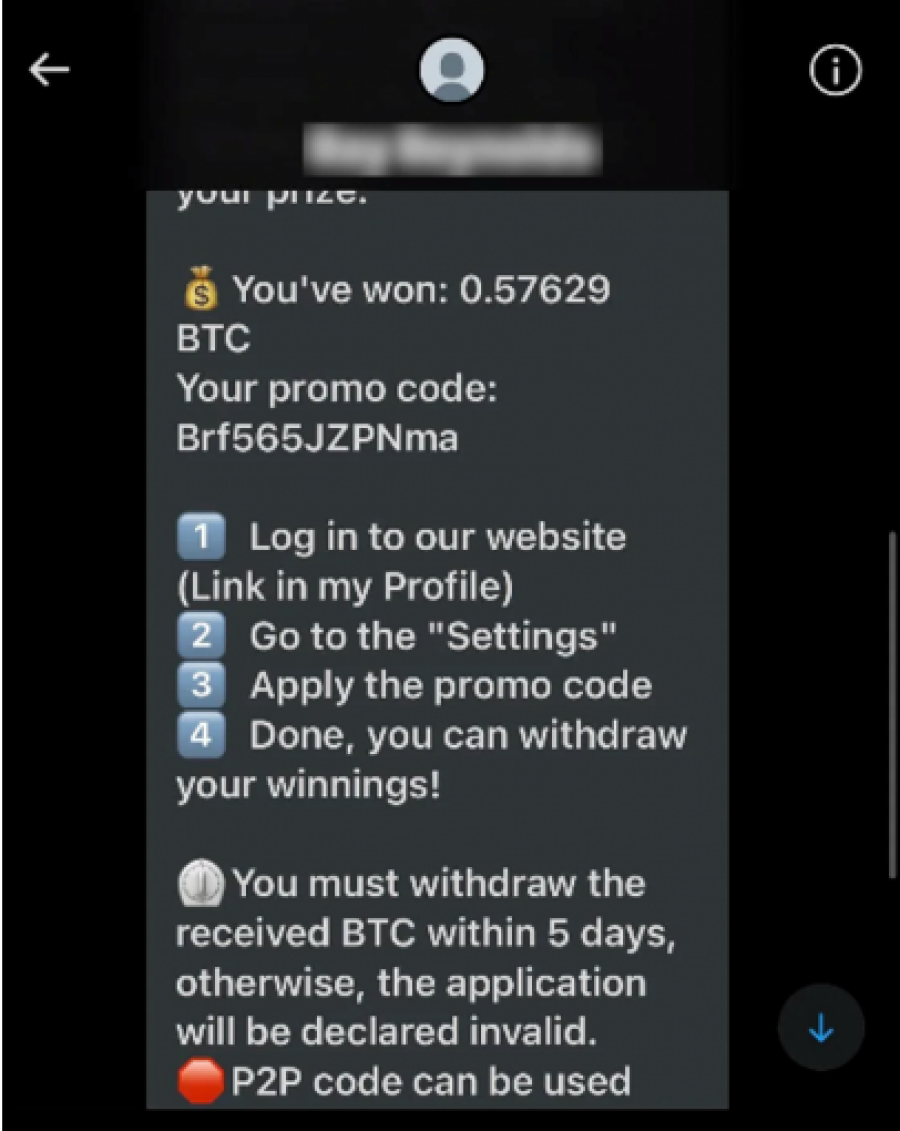
Scammers may try to steal people’s crypto, or use the allure of crypto as a way of getting people to part with their sensitive data, like in the example below.
Source: Reddit
This message claims the receiver has won just over $12,000 in Bitcoin and needs to log in to a
website to claim it. Websites such as this have been known to ask potential victims for all kinds
of personal data, including their usernames and passwords, full names, email addresses,
physical addresses, crypto wallet credentials, and more.
To keep your personal data and crypto safe, if you receive any unsolicited messages mentioning
cryptocurrency in any way, steer well clear.
#2 — Phishing Scams
The goal of Twitter phishing scams is to steal your Twitter username and password. If a hacker
were to gain access to your Twitter account, they could post inappropriate Tweets under your
name, message your friends and family while posing as you, read your personal messages, and
delete your pictures, videos, or even your Twitter account itself.

Twitter phishing email. Source: Twitter
Twitter phishing emails can take many forms, but they will often say there is a problem with your account and you need to urgently resolve it by clicking an included link. It’s the implied sense of urgency that almost always gives away a phishing scam. That, and the unofficial email address they’re often sent from (like in the example above). Emails from Twitter will only ever be sent from email addresses ending in @twitter.com or @e.twitter.com.
If you’re the owner of a verified Twitter account (one with a blue badge icon), you should check out this article because there are phishing scams specifically targeting you.
#3 — Celebrity Account Hacked Scams
The social media accounts of celebrities and public figures are prime targets for hackers. Those who’ve had their online accounts compromised include Joe Biden, Bill Gates, Kanye West, Elon Musk, Kim Kardashian, and many, many more.
What scammers love to do once they’ve gained control over a well-known individual or organization’s Twitter account, is to host fake crypto and NFT giveaways and raffles.
Back in May, popular NFT artist Beeple’s Twitter was hacked and the hackers ran a fake NFT raffle, requiring anyone wanting to participate to send them 1 ETH — cryptocurrency worth approximately $1,400. Although the hackers claimed all the money would be returned after the raffle had finished, we all know that was never going to be true.

Source: Twitter
Twitter Data Breach — 5.4 Million Users Affected
On July 20th, the data of over 5.4 million Twitter users was put up for sale on an underground internet forum for $30,000. The data set contains victims’ email addresses and phone numbers, despite whether they had configured their privacy settings to hide this information.
Although Twitter has since patched the vulnerability that led to this data breach, if you have a Twitter account you should be extra suspicious of phishing scams because hackers and scammers will use leaked data to conduct wide-scale scam campaigns.
Click here to learn how to enable two-factor authentication (2FA) on your Twitter account — essential for protecting against hackers. For complete instructions on how to do so, click here.
Twitter Scams — How to Stay Safe
- Be extra wary of messages received from strangers, and immediately delete anything referencing cryptocurrency or NFTs.
- Double-check that any emails sent to you by Twitter are genuine by confirming the email address ends in either @twitter.com or @e.twitter.com.
- Use Trend Micro Checkto protect you from scam websites, phishing links, and more — for FREE!
If you come across something dangerous online, Trend Micro Check — our 100% FREE browser extension and mobile app — will alert you in real time so you’ll know to stay well clear! Click the button below to learn more.
If you’ve found this article helpful, please do SHARE it with friends and family to help keep the online community secure and protected.
Source: pexels.com
Report a Scam!

Have you fallen for a hoax, bought a fake product? Report the site and warn others!
Scam Categories
Help & Info
Top Safety Picks
Your Go-To Tools for Online SafetyDisclaimer: Some of the links here are affiliate links. If you click them and make a purchase, we may earn a commission at no extra cost to you.
- ScamAdviser App - iOS : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on iOS
- ScamAdviser App - Android : Your personal scam detector, on the go! Check website safety, report scams, and get instant alerts. Available on Android.
- NordVPN : NordVPN keeps your connection private and secure whether you are at home, traveling, or streaming from another country. It protects your data, blocks unwanted ads and trackers, and helps you access your paid subscriptions anywhere. Try it Today!
- Incogni : Incogni automatically removes your personal data from data brokers that trade in personal information online, helping reduce scam and identity theft risks without the hassle of manual opt-outs. Reclaim your privacy now!
Popular Stories
As the influence of the internet rises, so does the prevalence of online scams. There are fraudsters making all kinds of claims to trap victims online - from fake investment opportunities to online stores - and the internet allows them to operate from any part of the world with anonymity. The ability to spot online scams is an important skill to have as the virtual world is increasingly becoming a part of every facet of our lives. The below tips will help you identify the signs which can indicate that a website could be a scam. Common Sense: Too Good To Be True When looking for goods online, a great deal can be very enticing. A Gucci bag or a new iPhone for half the price? Who wouldn’t want to grab such a deal? Scammers know this too and try to take advantage of the fact. If an online deal looks too good to be true, think twice and double-check things. The easiest way to do this is to simply check out the same product at competing websites (that you trust). If the difference in prices is huge, it might be better to double-check the rest of the website. Check Out the Social Media Links Social media is a core part of ecommerce businesses these days and consumers often expect online shops to have a social media presence. Scammers know this and often insert logos of social media sites on their websites. Scratching beneath the surface often reveals this fu
How do I recover my crypto after it’s stolen? What happens if your crypto wallet is compromised? Can stolen crypto be traced, and can police actually recover crypto in 2026? These are the questions most people ask within minutes of realizing their wallet has been drained. Crypto theft is fast, quiet, and unforgiving. By the time most victims notice something is wrong, the funds are already moving across the blockchain. Once seen as a problem for exchanges and whales, crypto theft now heavily affects everyday investors. Phishing links, fake support chats, wallet approval scams, SIM swaps, and malware attacks have become common. Knowing what recovery realistically looks like—and what it doesn’t—can prevent panic, bad decisions, and costly follow-up scams. In a Nutshell Crypto recovery is possible, but only in limited situations Blockchain transactions are irreversible, but stolen crypto can still be traced Speed and documentation matter more than optimism Police and exchanges play a bigger role than private recovery services Guaranteed recovery offers are almost always scams Is it Actually Possible to Recover Stolen Crypto? Yes, crypto recovery is possible, but only under specific conditions and rarely through direct action by the victim. Blockchain transactions are final by design. Once crypto is sent and confirmed, it cannot be reversed. There is no central authority, no chargeback process, and no technical “undo” button, even if the transaction was clearly fraudulent. This is where many people ask whether stolen crypto can be traced. In most cases, it can. Every transaction
